Research is expensive
We provide the information for bypassing the key for free. Research is expensive though, basically the time spent researching is overtime hours I do not get to work for pay. So if you like the work and want to say "thanks" feel free to make a small donation (or a large) to help cover the time I spent. It may help encourage me to make hacks to other versions of the software, though no promises :)
A walk through of cracking the Megatouch© Force 2011
Important note:All the steps below required you install the latest version of the Megatouch Force 2011.5 software.
Step 1: Obtaining access to the shell
The first step needed to crack the system is to get shell access to the system itself. The easiest way to do this is plug in a keyboard and override the Linux kernel boot configuration options to boot to run level 3- Using a Phillips head screwdriver remove the metal panel on the back of the megatouch, exposing the external USB port
- Plug in a USB keyboard into the USB port
- Turn on the machine, when you see the "FORCE" logo, hold down the "Alt" key, keep it held down till you see a red box on the screen and a console that says "boot:"
- Enter the following line
linux-V28_40 3 - Once the sytem is booted and prompting for a login, login with the following credentials
- username: maxx
- password: maxx
- You are now logged in as root
- Once you login you will most likely want to edit or copy files on the system. To do that you must first set the root filesystem (/) to read/write using the following command.
root@linux# mount -o remount,rw /
Step 2 - Obtaining the game code
On the Force 2011 the main game code is actually hidden with another binary. When the system starts, it launches /usr/local/bin/start. This code is just a wrapper program that contains and extracts the actual game binary. start extracts the real game binary from itself via /proc/self/exe, then it performs some decoding and finally writes the new program to disk as /tmp/dstart and launches the new binary. The details of the decoding are described here, however as you will see you do not actually need to understand how to decode the binary to retrieve the game code.While the designers of this code jump through a few hoops to try to hide the actual game binary, it is trivial to bypass all their work. Simply lauch /usr/local/bin/start and then copy out the decoded file from /tmp/dstart. To do this you must do the following steps.
- Patch out the code in /usr/local/bin/start that deletes /tmp/dstart
- this can be accomplished by overwriting 5 bytes of code with 0x90's at virtual memory address 0x8048b7d which is located at offset 0xb7d in the binary /usr/local/bin/start.
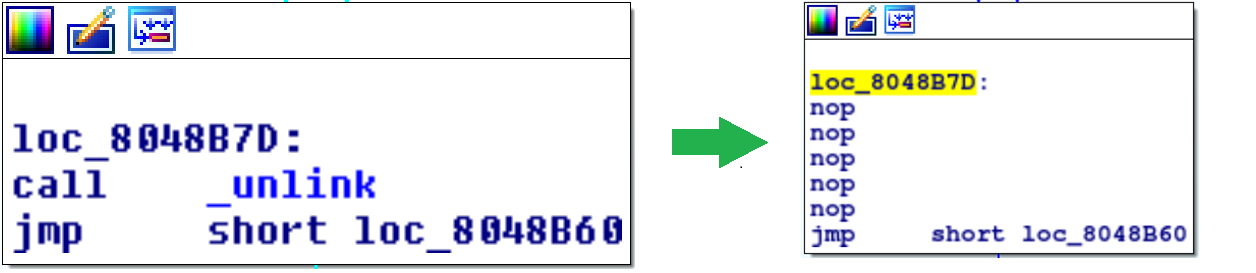
Here a command that will perform the patch
root@linux# perl -e 'print "\x90" x 5' | dd bs=1 count=5 seek=2941 of=/usr/local/bin/start conv=notrunc - Now launch /usr/local/bin/start. It will print some things to the screen and then crash, returning you to the command prompt.
-bash-3.00# /usr/local/bin/start - Once it crashes the file /tmp/dstart should be extracted. Move it to /tmp/extracted_dstart
*Note: If your wondering "couldn't I just have started the game normally and then copied /proc/<PID_of_dstart>/exe? The answer is yes, but the steps above were easier for me to write up.-bash-3.00# mv /tmp/dstart /tmp/extracted_dstart
Step 3: Replace /usr/local/bin/dstart
The next step is to replace the original /usr/local/bin/start binary with the binary you copied from /tmp/dstart. After you copy, ensure the SUID permission is set.The commands below will do this for you assuming your extracted file was called /tmp/extracted_dstart
-bash-3.00# cp /tmp/extracted_dstart /usr/local/bin/start
-bash-3.00# chmod 4755 /usr/local/bin/start

